Trusted Corporate Helpline 08003000963 Verified Tech Access
The trusted corporate helpline at 08003000963 offers a secure channel for workplace concerns and compliant guidance. Verified tech access introduces rigorous verification, audit trails, and least-privilege controls that protect systems and data. In incidents, disciplined containment and secure restoration follow documented playbooks. Strong authentication and ongoing monitoring underpin resilience and autonomy. This approach creates dependable operations, but questions remain about how best to integrate these practices across teams and technologies. Consider the implications for your organization’s security posture.
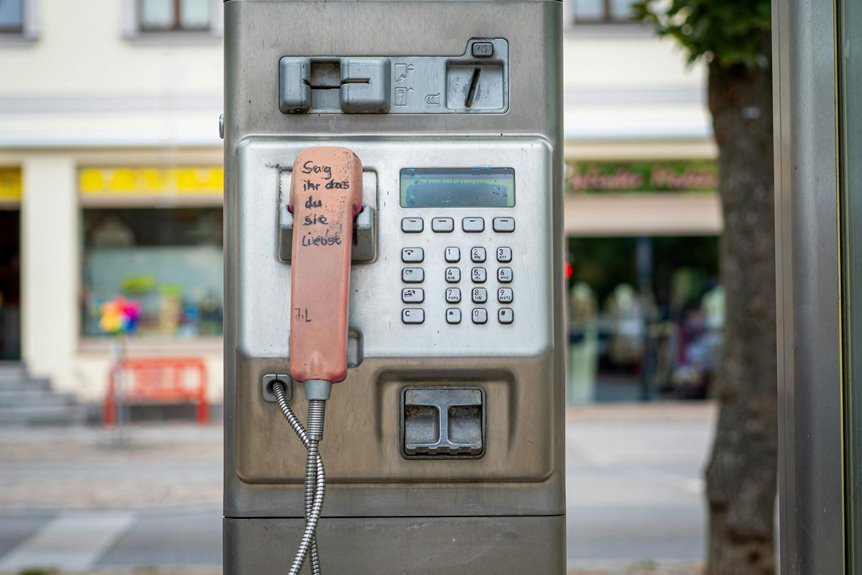
What Is the Trusted Corporate Helpline and Why It Matters
The Trusted Corporate Helpline is a designated support channel that connects employees with reliable, authority-approved assistance for workplace-related concerns. This trusted helpline offers clear guidance, reduces ambiguity, and reinforces compliance without compromising autonomy. It ensures secure corporate access, empowering individuals to raise issues confidently. By design, it sustains accountability, protects interests, and maintains operational integrity through authoritative, accessible support.
How 08003000963 Verifies Tech Access for Compliance
How does 08003000963 verify tech access to ensure compliance? The helpline implements rigorous compliance verification by auditing access control mechanisms, logging privilege changes, and enforcing least-privilege principles. It conducts periodic reviews of user entitlements and enforces authentication standards. By documenting control effectiveness, it sustains transparent accountability and aligns tech access with regulatory requirements, empowering organizations to uphold freedom through secure governance.
Steps for Immediate Incident Response and Access Recovery
Immediate incident response requires a disciplined, rapid sequence of actions to contain, eradicate, and recover access while preserving evidence. The protocol prioritizes decisive containment, targeted eradication of threats, and secure restoration of systems. Stakeholders implement documented playbooks, minimize downtime, and validate integrity. Training and audits reinforce readiness, ensuring incident response and access recovery align with governance, risk, and freedom-minded resilience.
Best Practices for Authentication and Data Protection
Effective authentication and data protection hinge on layered controls that deter unauthorized access and safeguard sensitive information.
Organizations should implement authentication best practices such as multi-factor authentication, regular credential audits, and principle of least privilege.
Data encryption shields data at rest and in transit, while robust key management sustains trust.
Continuous monitoring, rapid incident response, and clear policy articulation empower secure, freedom-enabled operations.
Conclusion
This article reinforces a unified stance: trusted helpline, trusted access, trusted operations. It emphasizes verification, transparency, and accountability; it emphasizes containment, eradication, and secure restoration. It emphasizes authorized reporting, authorized audits, and authorized reviews; it emphasizes least privilege, continuous monitoring, and layered protections. It emphasizes rapid guidance, rapid remediation, and rapid resilience. It emphasizes compliance, security, and trust. It emphasizes preparedness, partnership, and performance. In sum, credibility rests on clarity, control, and consistent consequence.