Web Portal Notes Documentation About Jeinzmacias .Com and Monitoring Logs

Web Portal Notes for Jeinzmacias.com clarify how pages organize access, data flows, and governance, distinguishing core navigation from ancillary discussions. The documentation outlines scope, structure, and practical guidance, emphasizing disciplined, freedom-focused governance and secure pathways. Monitoring logs underpin security, reliability, and incident response, providing centralized truth for authentication, changes, and performance. It sets up authentication, access, and change tracking, and explains how logs support incident response and troubleshooting, offering a concrete foundation that invites further exploration.
What Web Portal Notes Cover for Jeinzmacias.com
Web Portal Notes for Jeinzmacias.com outline the scope, structure, and purpose of the notes as they pertain to the site’s portal functions.
The document clarifies how pages organize access, data flow, and user roles, while distinguishing unrelated topic and off topic discussions from core navigation.
It promotes concise, practical guidance, avoiding ambiguity to empower freedom-focused, disciplined portal governance.
How Monitoring Logs Support Security and Reliability
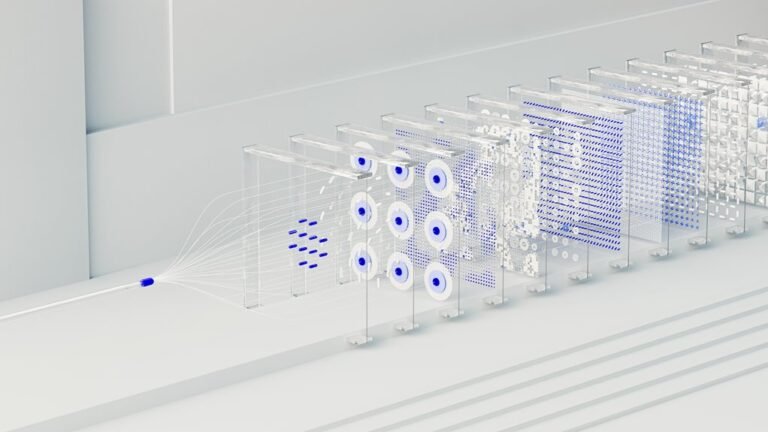
Monitoring logs function as a foundational element for both security and reliability within Jeinzmacias.com’s web portal. Their systematic collection enables data retention analysis, anomaly detection, and incident traceability, supporting proactive risk management.
Logs feed threat modeling, clarifying attack surfaces and resilience gaps. Consistent preservation, accessible review, and clear ownership reduce mean time to detection and restore service with confidence.
Setting Up Authentication, Access, and Change Tracking
An explicit access policy defines credentials, roles, and session limits, while change tracking captures every modification.
Audit events are time-stamped, immutable, and categorized to support accountability, diagnostics, and ongoing governance.
Using Logs for Incident Response and Performance Troubleshooting
Logs serve as a centralized source of truth for responding to incidents and diagnosing performance issues across the Jeinzmacias.com portal.
Logs enable structured incident response workflows, enabling rapid classification, containment, and remediation.
They support performance troubleshooting by correlating events, metrics, and timestamps.
Conclusion
The documentation on Jeinzmacias.com clarifies how access, data flows, and governance are structured, with monitoring logs forming the backbone of security, reliability, and incident response. It emphasizes disciplined governance, defined roles, and secure pathways, while logs provide a centralized truth for authentication, changes, and performance insights. A hypothetical case: after a suspicious login, logs enable rapid containment, trace the breach path, and restore services with minimal MTTR. This demonstrates the logs’ critical, real-world value.